2.3. String Vulnerabilities and Exploits | Secure Coding in C and C++: Strings and Buffer Overflows | InformIT

2.3. String Vulnerabilities and Exploits | Secure Coding in C and C++: Strings and Buffer Overflows | InformIT
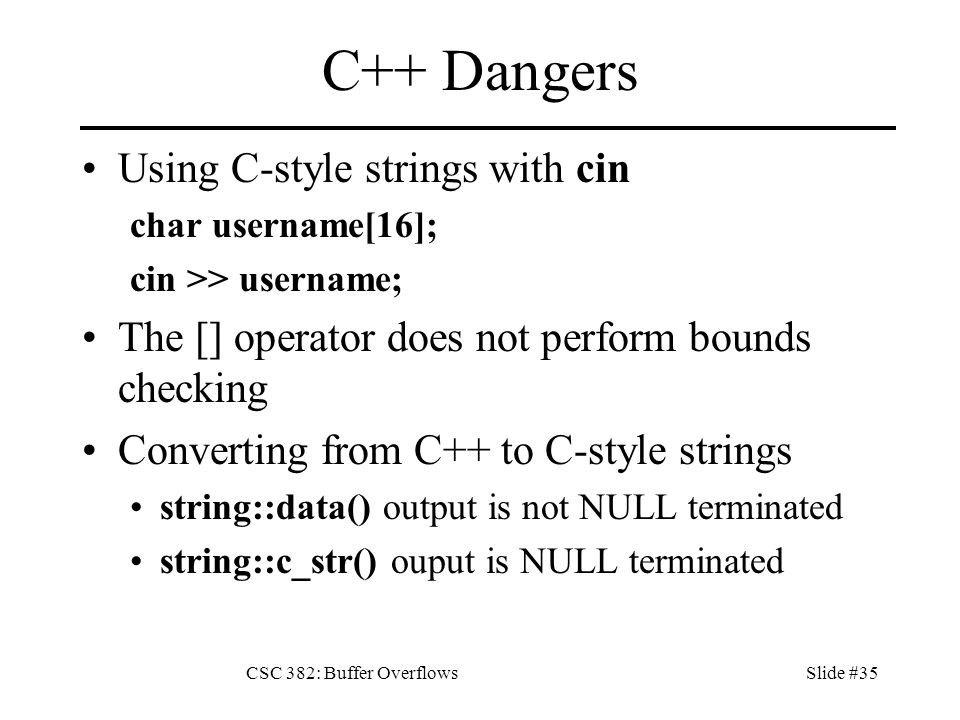
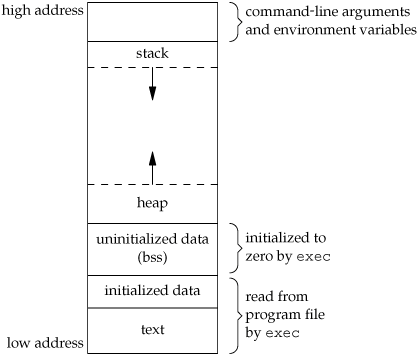
CSC 382: Buffer OverflowsSlide #1 Topics 1.What is a Buffer Overflow? 2.The Most Common Implementation Flaw. 3.Process Memory Layout. 4.The Stack and C's. - ppt download


![PDF] Automatic Removal of Buffer Overflow Vulnerabilities in C/C++ Programs | Semantic Scholar PDF] Automatic Removal of Buffer Overflow Vulnerabilities in C/C++ Programs | Semantic Scholar](https://d3i71xaburhd42.cloudfront.net/219eb813b257a30802b07990ac12019fe58479ca/9-Table7-1.png)